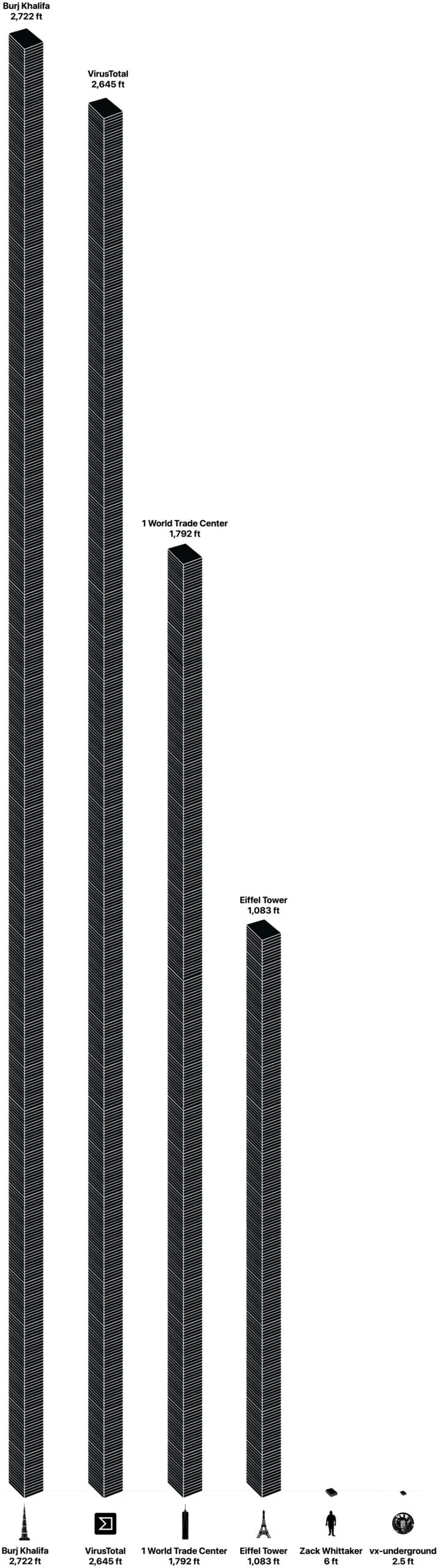
The digital battleground against cyber threats is characterized by an astronomical volume of data, a reality starkly illustrated by recent disclosures from leading malware research entities. vx-underground, a prominent malware research group that asserts it maintains the largest collection of malware source code globally, recently announced via a post on X that its extensive archive now totals approximately 30 terabytes (TB). This significant revelation was quickly followed by an even more staggering figure from Bernardo Quintero, the esteemed founder of VirusTotal. Quintero, whose online service is a cornerstone for scanning files against a multitude of antivirus engines simultaneously, reported that VirusTotal has accumulated an astounding 31 petabytes (PB) of malware samples contributed by users to date. To grasp the sheer magnitude of this difference, it’s crucial to note that one petabyte is roughly equivalent to 1,000 terabytes, placing VirusTotal’s repository on a scale exponentially larger than vx-underground’s. These colossal figures prompted an intriguing question within the cybersecurity community and beyond: what would these immense digital repositories look like if their data were physically stored on standard hard drives, stacked one upon the other, and how would they compare to iconic global landmarks like the Eiffel Tower or the Burj Khalifa?
The Unseen Battlefield: Why Malware Data Matters
In the modern era, data is the lifeblood of cybersecurity. The exponential growth in cyberattacks, coupled with their increasing sophistication, has transformed threat intelligence and defense into a data-intensive science. Repositories like those maintained by vx-underground and VirusTotal are not merely digital warehouses; they are indispensable laboratories for cybersecurity companies, artificial intelligence (AI) researchers, and threat intelligence firms. These vast datasets serve as the foundational bedrock for training advanced detection models, reverse-engineering malicious software, understanding the intricate evolution of attack methodologies, and ultimately, building more resilient digital defenses. Without such comprehensive collections, the ability to proactively identify and mitigate emerging threats would be severely hampered, leaving individuals, businesses, and critical infrastructure vulnerable.
- The Evolving Threat Landscape: The history of malware is a testament to constant innovation by malicious actors. From early viruses and worms to sophisticated ransomware, nation-state sponsored attacks, and advanced persistent threats (APTs), the complexity and volume of cyber threats have grown exponentially. Each new variant, each novel exploitation technique, adds to the collective knowledge required to combat them. This continuous arms race necessitates a dynamic and ever-expanding archive of malicious code and samples.
- Critical Role of Malware Repositories: Organizations like vx-underground and VirusTotal play a pivotal, albeit often behind-the-scenes, role in this defense. vx-underground’s focus on source code provides unparalleled insight into the fundamental design and intent of malware, enabling researchers to dissect its logic, identify common patterns, and develop more robust countermeasures. VirusTotal, on the other hand, with its massive collection of samples, offers a panoramic view of the threats actively circulating, providing real-time intelligence on new infections and the effectiveness of existing antivirus solutions. Both types of data are critical but serve distinct analytical purposes.
Giants of Digital Archiving: vx-underground and VirusTotal
Understanding the specific contributions of these two entities clarifies their unique significance in the cybersecurity ecosystem. While both deal with malware data, their focus and operational models differ considerably.
- vx-underground: Archiving the Genesis of Cyber Threats (Source Code)
vx-underground distinguishes itself by focusing on the source code of malware rather than just compiled samples. Source code represents the human-readable instructions written by programmers before being converted into executable programs. This focus provides an invaluable resource for deep analytical work. Researchers can study the code to understand programming logic, identify vulnerabilities that might be exploited by defenders, and even track the evolution of a particular malware family across different versions. A 30 TB archive of malware source code is an immense trove, offering a historical and technical blueprint of cyber threats. Cybersecurity experts widely acknowledge that access to such an extensive repository is instrumental for developing sophisticated behavioral analysis tools and advanced threat intelligence platforms. It allows for a forensic examination of malware’s inner workings, moving beyond mere detection to a profound understanding of its creation and capabilities. The group’s commitment to collecting and preserving this data underscores a belief in open research and collaboration within the cybersecurity community, providing a foundation for future defensive innovations. - VirusTotal: A Global Reservoir of Malware Samples
Bernardo Quintero’s brainchild, VirusTotal, operates on a different, yet equally critical, principle. It is an online service that enables users to upload suspicious files or URLs, which are then scanned by a multitude of antivirus engines and website scanners simultaneously. This crowdsourced model has allowed VirusTotal to amass an astonishing 31 petabytes of malware samples. Each submission, whether a new threat or a known variant, contributes to a continually growing global database of malicious indicators. This service acts as an early warning system, helping security researchers and IT professionals quickly assess threats and share intelligence. The sheer volume of data reflects the pervasive nature of malware and the constant stream of new infections worldwide. It offers a unique vantage point into global threat trends, geographical distribution of attacks, and the efficacy of various security solutions in real-time. The fact that users contribute this data voluntarily highlights the collaborative spirit vital for collective cyber defense. - Differentiating Source Code from Samples: A Crucial Distinction
The difference between vx-underground’s 30 TB of source code and VirusTotal’s 31 PB of samples is fundamental. Source code, while offering deep insights, is generally less voluminous than compiled binaries (samples) and their associated metadata. A single piece of malware source code might compile into many different samples depending on compilation options, packers, and obfuscation techniques. Conversely, 31 petabytes of samples represent an enormous diversity of executable files, documents, scripts, and other malicious artifacts, each potentially unique in its compiled form, even if derived from similar source code. This distinction underscores that both types of repositories are essential, complementing each other in the comprehensive fight against cybercrime. One provides the blueprint, the other provides the battlefield intelligence.
Visualizing the Invisible: From Terabytes to Towers

While the numbers 30 TB and 31 PB are abstractly large, their true scale becomes tangible when visualized in physical terms. The original article playfully imagined these datasets as stacks of hard drives, an exercise in "back-of-a-napkin" math that effectively communicates the monumental scale.
- The Methodology: Stacking Standard Hard Drives
To perform this visualization, a standard metric is needed. The calculation assumes the use of internal 3.5-inch hard drives, a common form factor for desktop computers and servers. These drives typically have a height of 1 inch. For simplicity, and acknowledging the "about" nature of the original data figures, each hard drive is assumed to hold exactly 1 terabyte of usable data, even though real-world usable capacity is often slightly less due to formatting overhead. This consistent unit allows for a direct conversion from digital capacity to physical height. - vx-underground’s Stack: A Manageable Footprint
With 30 terabytes of data, vx-underground’s repository would equate to 30 individual 1 TB hard drives. Stacked one on top of the other, these drives would reach a height of 30 inches, or approximately 2.5 feet. This is roughly the height of a small filing cabinet or a typical office desk. For a human perspective, this stack is notably smaller than the average person, illustrating that while 30 TB is a substantial amount of data for source code, its physical manifestation is surprisingly compact. - VirusTotal’s Colossus: Reaching for the Sky
The calculations for VirusTotal’s 31 petabytes are far more dramatic. Converting 31 petabytes to terabytes yields 31,744 terabytes (31 PB * 1024 TB/PB). Therefore, this data would require 31,744 hard drives. Stacked vertically, these drives would form a column an astounding 31,744 inches tall. Converting this to feet (dividing by 12 inches per foot), the stack would reach approximately 2,645 feet. This figure is staggering, almost reaching the clouds. - Landmark Comparisons: Eiffel Towers and the Burj Khalifa
To put 2,645 feet into context, consider some of the world’s most recognizable tall structures:- The iconic Eiffel Tower in Paris stands at 1,083 feet tall. VirusTotal’s data stack would be more than double its height, specifically about two-and-a-half times taller than the Eiffel Tower.
- One World Trade Center in New York City reaches 1,792 feet, meaning VirusTotal’s data tower would significantly surpass it.
- The Burj Khalifa in Dubai, currently the world’s tallest building, measures a colossal 2,722 feet. VirusTotal’s malware sample stack, at 2,645 feet, would stand almost shoulder-to-shoulder with this architectural marvel, falling short by a mere 77 feet. This proximity underscores the truly monumental scale of the data collected and managed by VirusTotal.
The visual contrast between vx-underground’s modest 2.5-foot stack and VirusTotal’s near-Burj Khalifa-sized tower vividly illustrates the vast difference between terabyte and petabyte scales, and the immense quantities of digital information being generated and collected in the ongoing fight against cybercrime.
The Strategic Imperative: Data’s Role in Modern Cybersecurity
Beyond the compelling physical visualization, these massive datasets represent a strategic imperative for global cybersecurity. Their existence and continuous growth are fundamental to developing effective defenses in an increasingly hostile digital environment.
- Fueling AI and Machine Learning in Threat Detection: The most profound impact of these vast repositories is their role in advancing artificial intelligence and machine learning (AI/ML) for threat detection. AI models require enormous quantities of data to learn, identify patterns, and make accurate predictions. Malware datasets provide the "training ground" for these algorithms. By feeding millions of malware samples (and benign files for contrast) into AI systems, researchers can train models to:
- Detect novel threats: Identify previously unseen malware variants based on their behavioral characteristics or code structure, rather than relying solely on known signatures.
- Improve anomaly detection: Distinguish between legitimate and malicious activity by understanding deviations from normal system behavior.
- Automate analysis: Speed up the process of reverse engineering and vulnerability assessment, reducing the time from threat emergence to defense deployment.
- Predict future attacks: By analyzing trends in malware evolution, AI can help predict the next generation of cyber threats.
- Understanding Attack Evolution and Predictive Intelligence: The historical depth of these datasets allows researchers to meticulously track the evolution of malware. This includes observing how attackers adapt their techniques, reuse code, exploit new vulnerabilities, and target specific industries or regions. Such longitudinal analysis is crucial for:
- Developing proactive defenses: Anticipating attacker moves rather than merely reacting to them.
- Identifying attacker groups: Linking different malware campaigns to specific threat actors based on shared code, infrastructure, or tactics.
- Informing policy and regulation: Providing data-driven insights for governments and organizations to craft more effective cybersecurity policies.
- The Challenge of Scale: Storage, Processing, and Analysis: While the benefits are immense, managing such colossal datasets presents significant logistical and technological challenges. Storing petabytes of data requires massive infrastructure, considerable energy consumption, and robust redundancy measures to prevent data loss. Processing this data—scanning, indexing, analyzing, and querying it—demands immense computational power, sophisticated distributed systems, and specialized algorithms. The sheer volume also necessitates advanced data curation techniques to ensure the quality, relevance, and accessibility of the information for researchers globally.
- Collaborative Defense: The Power of Shared Intelligence: The success of platforms like VirusTotal highlights the power of collaborative defense. By encouraging user contributions and sharing aggregated threat intelligence, these services foster a collective security posture. When one user uploads a new threat, the information immediately benefits countless others, accelerating detection and response across the globe. This model of shared intelligence is a critical component in leveling the playing field against highly organized and resourceful cyber adversaries.
The Future of Cyber Defense: An Ever-Growing Data Mountain
The trend is clear: the volume of malware data will only continue to grow. As technology advances, so too do the methods of cybercrime. The advent of AI-generated malware, polymorphic variants designed to constantly change their signatures, and fileless attacks that reside only in memory, will necessitate even larger and more diverse datasets to train the next generation of defensive technologies. The ability to collect, store, process, and analyze this ever-expanding digital mountain of malicious code and samples will remain a paramount concern for global cybersecurity.
In conclusion, the astounding physical scale of malware data, vividly illustrated by imagining stacks of hard drives reaching for the sky, underscores the invisible but monumental effort required to safeguard our digital world. The 30 terabytes of malware source code held by vx-underground and the 31 petabytes of malware samples collected by VirusTotal are not just abstract numbers; they are tangible representations of the relentless digital arms race. These colossal repositories are the indispensable arsenals of knowledge fueling AI-driven defenses, enabling researchers to understand attack evolution, and ultimately empowering humanity in the continuous battle against cybercrime. Their continued growth and effective utilization are non-negotiable for a secure future.