Nearly a week after Webpros, the makers of the ubiquitous web server management software cPanel and WebHost Manager (WHM), first alerted users to a critical flaw in its widely adopted platform, threat actors continue to actively target thousands of websites operating on the vulnerable software, perpetuating a significant cybersecurity crisis across the internet. The vulnerability, identified as CVE-2026-41940, enables attackers to seize full control of affected servers, posing an immediate and severe risk to data integrity and operational continuity for countless businesses and individuals.
The Persistent Threat: Scale and Scope of the Exploitation
As of Monday, the digital landscape reveals a sobering reality: over 550,000 servers globally remain potentially vulnerable, running versions of cPanel susceptible to this critical exploit. This alarming figure, meticulously tracked by Shadowserver, a non-profit organization dedicated to scanning and monitoring the internet for cyberattacks, has demonstrated an unsettling stability over several days, indicating a slow or incomplete patching effort across the vast cPanel ecosystem. While the number of actively compromised cPanel instances has seen a notable decrease from a peak of approximately 44,000 last Thursday to around 2,000 currently, the sheer volume of unpatched servers presents an enduring and attractive target for malicious actors. The fluctuating compromise figures underscore the dynamic nature of these attacks, where some systems may be cleaned, only for others to fall victim, or where detection methods evolve.
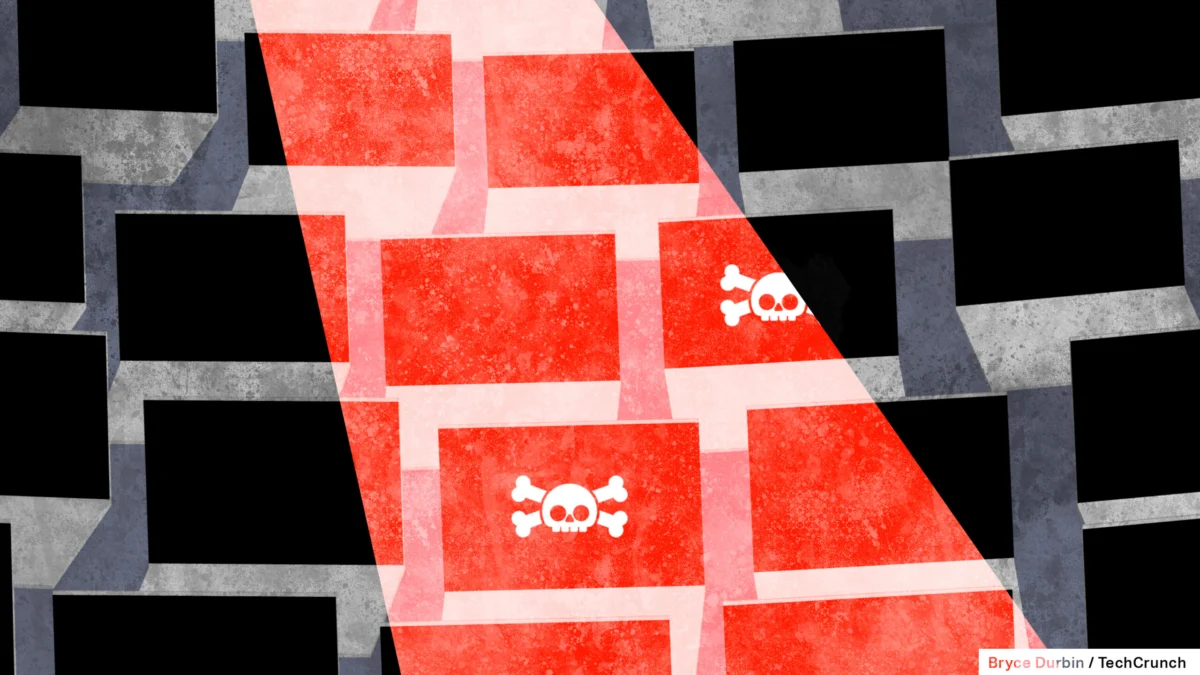
The ramifications of this vulnerability are profound, extending far beyond mere system disruption. Security researchers first sounded the alarm on Thursday, detailing how hackers had begun compromising servers running cPanel and WHM. The exploit leverages a critical bug that grants attackers complete administrative control over vulnerable servers via their control panels, effectively allowing them to hijack entire web presences. This level of access is the digital equivalent of handing over the keys to a kingdom, enabling attackers to deploy malware, steal data, deface websites, or, as observed in numerous instances, initiate ransomware attacks.
Ransomware Resurgence: The "Sorry" Campaign
One of the most immediate and visible consequences of this exploitation has been the widespread deployment of ransomware. As reported by Bleeping Computer, the scale of this damage is starkly illustrated by Google’s search index, which has cataloged dozens of websites that, at some point, displayed a chilling message from a group of hackers. This message unequivocally claimed the encryption of victim files in an apparent ransomware attack, demanding payment for their release. While some of these affected sites have since returned to normal operation, suggesting successful recovery or payment, the initial display of the ransom note—often including a unique chat ID for victims to negotiate with their digital captors—serves as a grim testament to the vulnerability’s destructive potential. TechCrunch’s attempts to solicit comment from the ransomware operators via the provided chat IDs did not yield an immediate response, a common tactic employed by such groups to maintain anonymity and control the communication channel.
Ransomware attacks, such as the "Sorry" campaign observed here, typically involve malicious software encrypting a victim’s files, rendering them inaccessible. Attackers then demand a ransom, usually in cryptocurrency, in exchange for a decryption key. The financial and reputational costs for affected organizations can be immense, ranging from direct ransom payments to significant downtime, data loss, and recovery expenses. For many small and medium-sized businesses (SMBs) that rely on cPanel-managed hosting, such an attack can be existential.
Chronology of a Critical Exploit
The timeline of CVE-2026-41940 underscores the rapid transition from discovery to widespread exploitation, a common yet concerning pattern in modern cybersecurity:
- February 23, 2026 (or earlier): Evidence suggests that initial attacks against web servers running cPanel and WHM began much earlier than the public disclosure. Daniel Pearson, CEO of KnownHost, a prominent web hosting provider, reported that his company detected attacks leveraging this vulnerability as far back as this date, indicating a period of stealthy exploitation before the flaw was widely known.
- Early April 2026: cPanel (Webpros) privately identifies and begins to address the critical vulnerability.
- April 29, 2026: cPanel officially releases patches and issues an initial security advisory to its users, urging immediate updates.
- April 30, 2026: Security researchers and news outlets, including TechCrunch, begin to report on active exploitation of the bug, confirming that hackers are compromising servers. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issues a public warning, adding CVE-2026-41940 to its Known Exploited Vulnerabilities (KEV) catalog. This designation signifies that the vulnerability is actively being exploited in the wild and poses a significant risk to federal civilian executive branch (FCEB) agencies. CISA mandates that government agencies patch this vulnerability by Sunday, May 3, 2026, highlighting the urgency and severity of the threat.
- May 1-3, 2026: Active exploitation continues, with a peak in detected compromised instances. Ransomware campaigns become more visible.
- May 4, 2026 (Monday): Shadowserver reports over 550,000 potentially vulnerable servers still active, with around 2,000 instances confirmed compromised, down from the peak but still a substantial number. The persistent high count of vulnerable systems indicates a significant challenge in widespread remediation.
Official Responses and Industry Vigilance
The U.S. Cybersecurity and Infrastructure Security Agency (CISA)’s swift action in adding CVE-2026-41940 to its KEV catalog underscores the gravity of the situation. The KEV catalog is a definitive list of vulnerabilities that CISA believes pose a significant risk to federal networks and critical infrastructure, requiring urgent patching. While CISA did not immediately respond to inquiries regarding whether government agencies had successfully patched their servers by the Sunday deadline, their directive serves as a strong signal to all organizations about the imperative of immediate action.
Webpros, the company behind cPanel and WHM, which proudly states its software powers an astounding 60 million domains globally, has remained tight-lipped following the initial security advisory. Executives did not respond to requests for comment regarding the ongoing exploitation or the slow rate of patching among its vast user base. This silence, while perhaps strategic, leaves a void in public communication at a critical time when clearer guidance and stronger calls to action could be beneficial.
The early detection by KnownHost’s CEO Daniel Pearson highlights the proactive role that some hosting providers play in identifying and mitigating threats. Such early warnings, even if initially internal, are crucial for rapid response within the hosting community. However, the fragmented nature of the web hosting industry means that not all providers possess the same level of sophisticated threat detection capabilities, leading to varied response times and vulnerability windows.
The Ubiquity of cPanel: A Double-Edged Sword
To understand the full impact of this vulnerability, it is essential to appreciate the critical role cPanel and WHM play in the internet’s infrastructure. cPanel is a widely used graphical user interface (GUI) that simplifies the process of managing websites and hosting accounts. Paired with WebHost Manager (WHM), which provides administrative control over server settings, it forms the backbone for millions of shared hosting, VPS (Virtual Private Server), and dedicated server environments worldwide. From small business websites and personal blogs to e-commerce platforms and institutional portals, a significant portion of the internet relies on the ease of use and comprehensive features offered by cPanel.
This widespread adoption, while a testament to the software’s utility, also makes it a prime target for attackers. A vulnerability in cPanel isn’t just a flaw in one piece of software; it’s a potential gateway into hundreds of thousands, if not millions, of individual websites hosted on those servers. This creates a "supply chain" risk where a single vulnerability can have cascading effects across the internet.
Challenges in Patching and Mitigation
The persistent number of vulnerable servers, despite public warnings and available patches, points to several systemic challenges in the broader cybersecurity landscape:
- Awareness and Communication: Not all server administrators or website owners may be immediately aware of the vulnerability or the urgency of the patch, especially if they rely on managed hosting where updates might be handled by third parties, or if they operate older, less actively maintained systems.
- Complexity of Updates: While cPanel strives for easy updates, the process can sometimes be complex, requiring downtime or specific technical expertise, especially for highly customized server configurations.
- Legacy Systems: A significant portion of the internet still runs on older software versions. Upgrading entire server environments can be a costly and time-consuming endeavor, leading to a reluctance to patch unless absolutely necessary, or until forced by catastrophic events.
- Managed vs. Unmanaged Hosting: In managed hosting environments, the hosting provider is responsible for server maintenance and patching. However, in unmanaged or self-managed VPS/dedicated server setups, the onus falls entirely on the client, who may lack the expertise or resources to act promptly.
- Attacker Agility: Threat actors are often highly agile, developing exploits rapidly once a vulnerability is disclosed, sometimes even before official patches are widely deployed and applied. This "patch gap" or "window of vulnerability" is a critical period for attackers.
Broader Implications for Cybersecurity
The cPanel vulnerability and its ongoing exploitation highlight several critical implications for global cybersecurity:
- Supply Chain Risk: The incident underscores the inherent risks associated with widely adopted infrastructure components. A flaw in a foundational piece of software like cPanel can ripple through the entire digital supply chain, affecting numerous downstream users who may not even be aware of the underlying technology.
- Importance of Proactive Security: The early detection by KnownHost illustrates the value of robust, proactive security monitoring and threat intelligence sharing within the industry. Relying solely on vendor patches after public disclosure often leaves a critical window for exploitation.
- User Responsibility: While vendors are responsible for developing secure software, users and hosting providers bear the ultimate responsibility for applying patches and maintaining secure configurations. This incident serves as a stark reminder for all stakeholders to prioritize security updates.
- The Persistent Threat of Ransomware: Ransomware continues to be a dominant threat vector, constantly evolving and targeting new vulnerabilities. The "Sorry" campaign against cPanel servers demonstrates its adaptability and destructive potential.
- The Need for Resilience: Organizations must not only focus on prevention but also on resilience. Robust backup and recovery strategies are crucial for mitigating the impact of successful ransomware attacks and ensuring business continuity.
Recommendations and Best Practices
For those operating cPanel/WHM servers or hosting websites on such platforms, immediate action remains paramount:
- Patch Immediately: Ensure that cPanel and WHM installations are updated to the latest secure versions as advised by Webpros. Verify that the patches for CVE-2026-41940 have been successfully applied.
- Verify Integrity: After patching, conduct a thorough scan of the server for any signs of compromise, including unauthorized files, suspicious processes, or unusual network activity. Check website files for defacement or injected malicious code.
- Implement Strong Access Controls: Review and strengthen all login credentials, especially for cPanel/WHM and SSH access. Use strong, unique passwords and enable Two-Factor Authentication (2FA) wherever possible.
- Regular Backups: Maintain regular, off-site, and immutable backups of all website data and server configurations. These backups are critical for recovery in the event of a successful ransomware attack.
- Monitor Server Logs: Actively monitor server logs for any suspicious activity, failed login attempts, or unauthorized access.
- Network Segmentation: Where feasible, implement network segmentation to limit the lateral movement of attackers within a compromised environment.
- Web Application Firewall (WAF): Utilize a WAF to protect web applications from common attack vectors and provide an additional layer of security.
- Stay Informed: Continuously monitor security advisories from cPanel, CISA, and reputable cybersecurity news outlets for new threats and patches.
The ongoing exploitation of the cPanel vulnerability is a potent reminder of the relentless nature of cyber threats and the critical importance of a proactive, multi-layered approach to cybersecurity. While the number of actively compromised servers has decreased, the persistent half-million vulnerable systems represent an unacceptable risk, underscoring the urgent need for comprehensive patching and heightened vigilance across the entire cPanel user base. The internet’s stability and the security of its vast array of digital services hinge on the collective commitment to addressing such critical vulnerabilities swiftly and decisively.